Modern and secure WiFi network in 23 branches – how did we do it?
One of our first actions for the client, where we began implementing comprehensive IT support, was to ensure a secure WiFi system. The client has 23 publicly accessible facilities. The WiFi network was secured only with a simple password (WPA2), and the network key was publicly known. The WiFi network was not subject to any restrictions; it was merely separated from the client's production network. As a result, anyone could access the internet without restrictions. Unfortunately, in the past, this network was used to commit cybercrime. Securing it was crucial.
One of our first actions for the client, where we began implementing comprehensive IT support, was to ensure a secure WiFi system.
The client has 23 publicly accessible facilities. The WiFi network was secured only with a simple password (WPA2), and the network key was publicly known. The WiFi network was not subject to any restrictions; it was merely separated from the client's production network. As a result, everyone could access the internet without restrictions. Unfortunately, in the past, this network was used to commit cybercrime. Securing it was crucial.
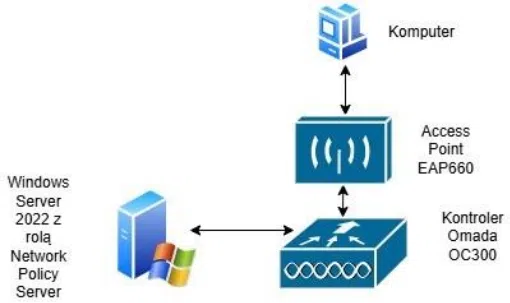
We proposed a secure and modern solution based on the TP-Link Omada OC300 controller and TP-Link EAP660 HD access points, which enabled:
- Creating a separate, encrypted Wi-Fi network for employees using the WPA Enterprise IEEE 802.1X standard, based on a Windows Network Policy Server authorization server.
- Launching a public (guest) network on a dedicated VLAN, separated from the employee network, which can be accessed via a voucher portal.
How was the implementation carried out?
We began by replacing old switches and installing new access points. We configured the Omada OC300 controller and prepared the server environment.
Employee Network – Maximum Security
We created a separate Wi-Fi network for employees, using one of the most secure authentication methods, EAP-TLS. It is widely used in corporate environments where security is a priority. This method uses digital certificates to mutually authenticate the client and server, eliminating the risk of attacks. Thanks to this:
- Only computers with appropriate certificates have access to this network,
- All data transferred between the client and server is encrypted,
- There is no risk of password leakage.
We used a Windows Network Policy Server (NPS) to handle authorization, acting as a RADIUS server. In the Active Directory environment, we implemented GPO policies that automatically install certificates on employee computers, ensuring Wi-Fi connections are automatic and require no typing.
How does WPA Enterprise work with EAP-TLS?
1 397
Guest Network – Controlled Access via Voucher
We've launched an open WiFi network with a voucher portal for guests and clients. How does it work?
- After connecting to the network, users see a login page.
- To gain internet access, they must enter a one-time code (voucher).
- The codes are time-limited and can be used only once or for a specified number of times.
- The administrator can see who used the network and when.
Additionally:
- The network operates on a separate VLAN, meaning it's physically separated from the employee network.
- Non-standard ports have been blocked to prevent abuse.
- Traffic shaping has been implemented to protect facilities from connection overload.
The end result – security and complete control
Thanks to the implementation:
- The employee network is fully secured, password-free, with encrypted communication.
- Guests use the internet only with permission, and all access is logged.
- The company has gained complete control and security, eliminating the risk of unauthorized access or illegal activity.
This solution is ideal for companies and institutions with multiple locations who want to ensure their Wi-Fi network operates securely, stably, and in accordance with best practices.
If you would like to implement a similar solution in your company, please contact us. We'd be happy to help!
our
support.
An IT company, or IT firm, deals with information technology in a broad sense. This includes, among other things:
- Software design and development: An IT company can create custom applications for other companies or software products for the mass market. Depending on their specialization, these can include mobile applications, desktop applications, web applications, or embedded systems.
- Consulting services: An IT company often provides experts to advise on implementing new technologies, optimizing business processes, or selecting appropriate technological solutions.
- Cloud solutions: Many IT companies specialize in implementing and managing cloud solutions, such as data storage, application hosting, and data analysis platforms.
- IT security: Protection against cyberattacks, security audits, implementing security policies, and network monitoring are just some of the IT companies' responsibilities in this area.
- IT infrastructure management: In this area, a company may manage servers, databases, networks, and endpoints.
- Technical Support and Service: An IT company may provide support for its own products or general IT support for other companies, managing their technology on a daily basis.
- Training: Many IT providers also offer training in software use and secure technology use.
- Hardware Solutions: Some IT companies may also provide and configure computer, server, or network hardware.
Depending on their specialization and size, an IT company may offer one, several, or all of the above solutions. When choosing a provider, it's important to thoroughly understand their services and tailor them to your individual needs.
At Support Online, we have been supporting companies for years with
- comprehensive user support (both on-site and remotely),
- we service computers, phones, tablets, and related network issues,
- we specialize in server administration: Windows, Linux/Unix,
- we support virtualizers such as KVM, Hyper-V, VMWare, and Proxmox,
- we support cloud services, particularly solutions such as Azure, Microsoft 365, and AWS,
- we monitor servers and devices on the internet,
- we consult on development, DRP, and support the stability of your business in the IT layer.
If you're looking for a good IT company, Support Online is the right place to grow your business.
It's worth using an IT company like Support Online when:
- You plan to implement new technologies or software in your company.
- You need specialized technology consulting.
- You want to optimize existing IT processes.
- You struggle with digital security issues.
- You need support in managing your IT infrastructure.
- You lack internal resources or expertise to implement certain technology projects.
Using external IT experts can bring benefits in terms of saving time and resources, and ensuring high-quality solutions.
Hiring an IT company like Support Online offers several key benefits over an IT freelancer:
- Support from the entire team: An IT company has a full team of specialists, from DevOps specialists and Cyber Security Specialists to IT Helpdesk Specialists, who possess diverse skills and experience, enabling faster problem resolution and the implementation of more complex projects.
- Reliability and stability: IT companies have an established reputation and track record, which can translate into greater reliability and stability of services.
- Maintenance and support: An IT company can offer service contracts, warranties, and after-sales support, which may be more difficult to obtain from an individual freelancer.
- Resources: Companies have access to more resources, tools, and technologies that can accelerate and improve project execution.
- Long-term availability: The risk of a freelancer disappearing or changing careers is greater than the risk of a well-established company going out of business.
However, it's worth noting that the choice between a company and a freelancer depends on your specific needs and situation. If you value peace of mind and a quick response to unexpected problems, it is worth choosing an IT company such as Support Online.
Partnering with IT Support Online offers the following advantages:
- Professional IT outsourcing: The company guarantees high-quality IT outsourcing services for businesses of all sizes.
- Comprehensive IT support: IT Support Online provides comprehensive IT support that meets the diverse needs of businesses.
- Saves time and money: With our support, clients can focus on their core business activities while reducing the costs associated with information technology management.
- Serving a diverse range of businesses: The company specializes in serving both small and medium-sized enterprises and large corporations, demonstrating its flexibility and ability to adapt to diverse client needs.
- Leadership in IT outsourcing: The company is recognized as a leader in IT outsourcing, particularly in the Poznań and Warsaw regions.
By partnering with our company, IT Support Online, businesses can count on a high standard of service and professionalism at every stage of the relationship.



